Why Cybersecurity Requires Specialized Industrial Computers
Cybersecurity applications demand hardware that is both powerful and secure at the foundation level. Unlike consumer PCs, industrial computers for cybersecurity must support hardware-level security features such as Trusted Platform Module (TPM), secure boot, and virtualization-based security. They also need to run 24/7 in demanding environments—whether in network operations centers (NOCs), security operations centers (SOCs), or industrial control system (ICS) perimeters—without overheating or failing. Fanless, rugged designs reduce points of failure and electromagnetic interference, making them ideal for sensitive security deployments.
Key Specifications for Secure Industrial PCs
When selecting a PC for cybersecurity, prioritize processors with integrated security technologies. Intel® Core™ i5 and i3 processors (12th Gen and newer) include Intel® Hardware Shield, which provides built-in security features like OS-hardening below the operating system layer. For cybersecurity analysis tools, a minimum of 8GB RAM is recommended, with 16GB or more for running multiple virtual machines or packet capture applications. Storage should be SSD-based (256GB or higher) for fast boot times and data access. Additionally, dual Ethernet ports are valuable for setting up network taps or isolated security zones.
Use Cases and Applications
Secure industrial computers are deployed in several cybersecurity scenarios:
-
Network Security Appliances: Running firewalls, intrusion detection/prevention systems (IDS/IPS), and unified threat management (UTM) software.
-
Security Operations Centers (SOCs): Hosting SIEM platforms, threat intelligence feeds, and forensic analysis tools.
-
Industrial Control System (ICS) Security: Monitoring and protecting SCADA networks, programmable logic controllers (PLCs), and other operational technology (OT) assets.
-
Penetration Testing and Red Teaming: Portable, rugged machines for on-site security assessments.
-
Data Diode and Air-Gap Solutions: Securely transferring data between classified and unclassified networks.
Comparison of Cybersecurity-Ready Configurations
| Feature | Entry-Level (e.g., N100) | Mid-Range (e.g., i3-1215U) | High-Performance (e.g., i5-1240P) |
|---|---|---|---|
| Processor | Intel N100 (4 cores) | Intel i3-1215U (6 cores) | Intel i5-1240P (12 cores) |
| RAM | 4-8GB | 8-16GB | 16-32GB |
| Storage | 128-256GB SSD | 256-512GB SSD | 512GB+ SSD |
| TPM Support | Yes (firmware TPM) | Yes (discrete TPM option) | Yes (discrete TPM option) |
| Use Case | Lightweight firewall, log collector | SIEM agent, basic IDS | Full SOC platform, VM host |
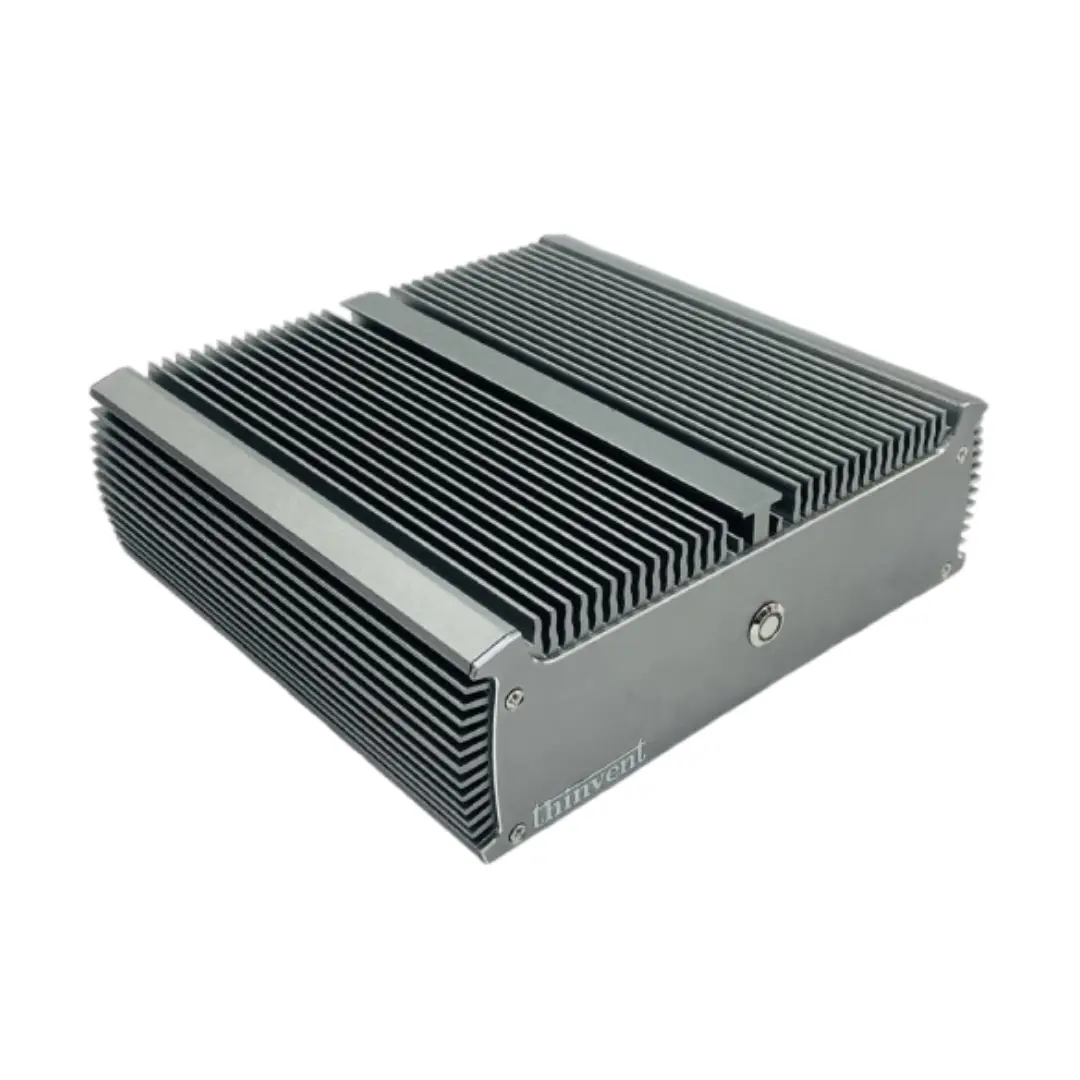
Thinvent's Products for Cybersecurity
Thinvent offers a range of industrial computers purpose-built for cybersecurity applications. Our Industrial PC IPC3 (Intel Core i3-1215U, 8GB RAM, 256GB SSD) and Industrial PC IPC5 (Intel Core i5-1240P, 16GB RAM, 512GB SSD) feature fanless designs, wide temperature tolerance, and support for Linux (Ubuntu) or Windows IoT operating systems—ideal for hardened security deployments. For environments requiring minimal power consumption, our Treo Mini PC with Intel N100 processor provides a cost-effective, secure platform for dedicated security tasks. All models support TPM 2.0 and secure boot, ensuring a trusted computing base from power-on.